Cyber Security Awareness Month
PCC participates in National Cybersecurity Awareness Month (NCSAM) each year by providing tips and tools for reducing cybersecurity risks and protecting yourself online.
Phishing
Phishing attacks use email or malicious websites to infect your machine with malware and viruses to collect personal and financial information. Cybercriminals attempt to lure users to click on a link or open an attachment that infects their computers, creating vulnerability to attacks. Phishing emails may appear to come from a real financial institution, e-commerce site, government agency, or any other service, business, or individual. The email may also request personal information such as account numbers, passwords, or Social Security numbers. When users respond with the information or click on a link, attackers use it to access users’ accounts.
How criminals lure you in
“Never click suspicious links in emails or text messages. Use caution when opening email attachments, especially password-protected zip files. Malicious software or Malware can be found in email attachments.” inspiredelearning.com
The following messages from the Federal Trade Commission’s OnGuardOnline are examples of what attackers may email or text when phishing for sensitive information:
- “We suspect an unauthorized transaction on your account. To ensure that your account is not compromised, please click the link below, and confirm your identity.”
- “During our regular verification of accounts, we couldn’t verify your information. Please click here to update and verify your information.”
- “Our records indicate that your account was overcharged. You must call us within 7 days to receive your refund.”
Simple tips

Text description – spear phishing
Spear phishing: A targeted scam directed at a specific person or department.
- Spot: The email sender appears to be a campus administrator.
- Verify: Ensure that the sender account is @pcc.edu
- Stop: Report the phish and don’t respond.
- Maintain: Keep separate work and personal accounts.
- Play hard to get with strangers. Links in email and online posts are often the way cybercriminals compromise your computer. If you’re unsure who an email is from – even if the details appear accurate – do not respond, and do not click on any links or attachments found in that email. Be cautious of generic greetings such as “Hello Bank Customer,” as these are often signs of phishing attempts. If you are concerned about the legitimacy of an email, call the company directly.
- Think before you act. Be wary of communications that implore you to act immediately. Many phishing emails attempt to create a sense of urgency, causing the recipient to fear their account or information is in jeopardy. If you receive a suspicious email that appears to be from someone you know, reach out to that person directly on a separate secure platform. If the email comes from an organization but still looks “phishy,” reach out to them via customer service to verify the communication.
- Protect your personal information. If people contacting you have key details from your life – your job title, multiple email addresses, full name, and more that you may have published online somewhere – they can attempt a direct spear-phishing attack on you. Cybercriminals can also use social engineering with these details to try to manipulate you into skipping normal security protocols.
- Be wary of hyperlinks. Avoid clicking on hyperlinks in emails and hover over links to verify authenticity. Also, ensure that URLs begin with “https.” The “s” indicates encryption is enabled to protect users’ information.
- Double your login protection. Enable multi-factor authentication (MFA) to ensure that the only person who has access to your account is you. Use it for email, banking, social media, and any other service that requires logging in. If MFA is an option, enable it by using a trusted mobile device, such as your smartphone, an authenticator app, or a secure token—a small physical device that can hook onto your key ring. Read the how-to guide for multi-factor authentication for more information.
- Shake up your password protocol. According to NIST guidance, you should consider using the longest password or passphrase permissible. Get creative and customize your standard password for different sites, which can prevent cybercriminals from gaining access to these accounts and protect you in the event of a breach. Use password managers to generate and remember different, complex passwords for each of your accounts. Read the creating a password tip sheet for more information.
- Install and update anti-virus software. Make sure all of your computers, Internet of Things devices, phones, and tablets are equipped with regularly updated antivirus software, firewalls, email filters, and anti-spyware.

Text description – don’t get hooked
Be on the lookout for the tell-tale signs of a phishing email, before you click! Following these basic steps can help protect your company and customers.
- Be cautious. Always be careful when using email. Follow the necessary precautions before clicking links or opening attachments.
- Spelling errors. Spelling errors are another indication. Many phishing emails contain strange phrasing and poor grammar. Attackers will often hastily send emails to numerous recipients, hoping to “cast a wide net” and trick an unsuspecting person.
- Urgent action. Watch out for calls to action with a deadline or a suggested consequence aimed at creating panic. Attackers use time-sensitive and threatening language to increase the chance of clicking.
- Verify links. Phishing attempts may contain a link that appears to be legitimate. Double-check by simply hovering your mouse over the link to see the actual URL.
- “From:” address. The “From:” address of an email can be forged to appear legitimate. Attackers can slip a small typo into an email address to make it look like it’s from a legitimate source, such as a CEO or your bank.
- Personal information. Emails requesting personal information are always suspect. Follow the previous steps before providing usernames, passwords, or other personal or company proprietary information.
Follow these general steps every time you receive an email to prevent being hooked by a phishing scheme.
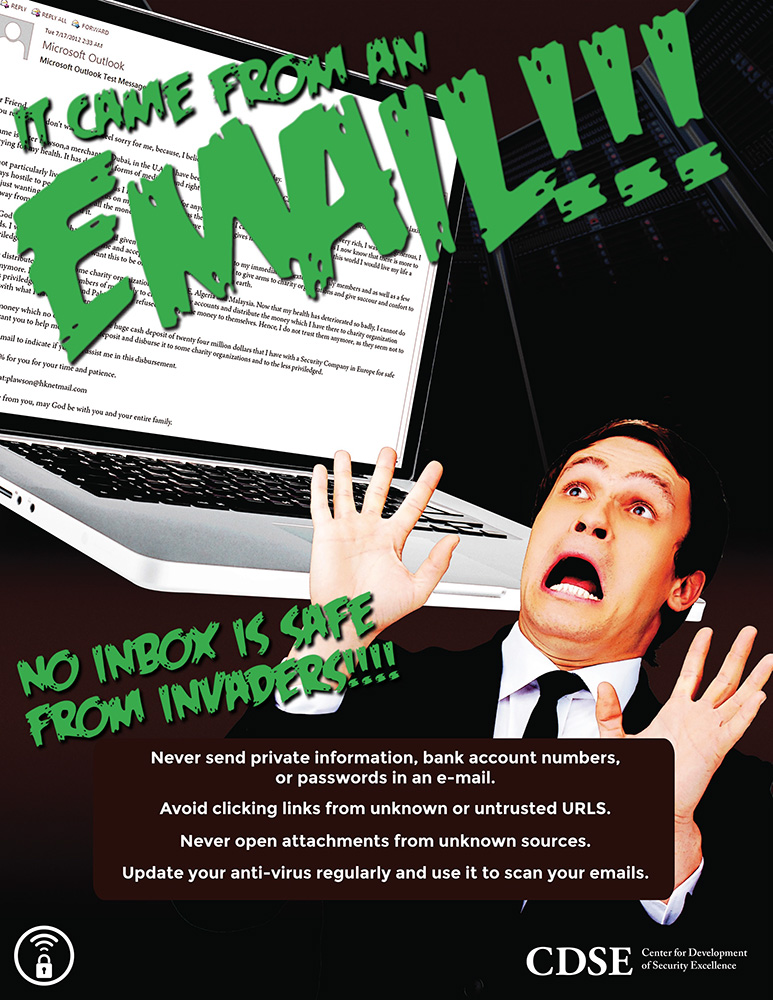
Text description – it came from an email
It came from an email! No inbox is safe from invaders!
- Never send private information, bank account numbers, or passwords in an email.
- Avoid clicking links from unknown or untrusted URLs.
- Never open attachments from unknown sources.
- Update your anti-virus regularly and use it to scan your emails.
Tip sheets
- A how-to guide for multi-factor authentication
- Creating a password
- Social media cybersecurity
- Phishing
- Phishing emails sometimes pose as queries from legitimate businesses. If an email looks suspicious, contact the sender directly before clicking on links or opening attachments.
- You may not always be able to detect a phishing attack. If you believe you have fallen victim, contact your IT department.
- You’ve been fished (NIST video)
Do your part: #BeCyberSmart

